Simplify Your Azure AD B2C User Management
Managing Azure AD B2C users doesn’t have to be complicated. I've created an online or on prem service to manage Azure AD B2C users. With Attribute Editor, you get an intuitive, powerful tool to handle custom user attributes effortlessly.
Learn More or Contact Me for assistance with your Azure AD B2C project.
This is a blog post on how to get the full list of custom attributes that exist in an Azure B2C tenant. This example uses Microsoft Graph API and the client credentials OAuth flow.
Register the Graph API app
The first thing is sign into your Azure B2C tenant and create a new app registration for the Graph API app. This example uses a separate Azure App Registration to connect to the Graph API. You could use an existing Azure App if you wanted to as well. These instructions are similar to the set up that for getting a list of users for a B2C tenant. Follow these steps to create a new Graph API app in your Azure environment if you have not already done so.
- Switch to your B2C Tenant directory
- Go to Azure AD B2C
- Select App registrations in the Manage section
- Create a New registration
- Give your app a name. I named mine B2C Graph API. Click save and make a copy of the newly created Client Id.
- Click Certificates & secrets and create a New client secret. Give it a descriptive name and set the expiration date. I usually set mine to 6 months.
- Copy the Value of the newly created secret and hold on to it. Store the value in a secret vault or other safe place along with the client id from step 5.
Get an access token for the Graph API app
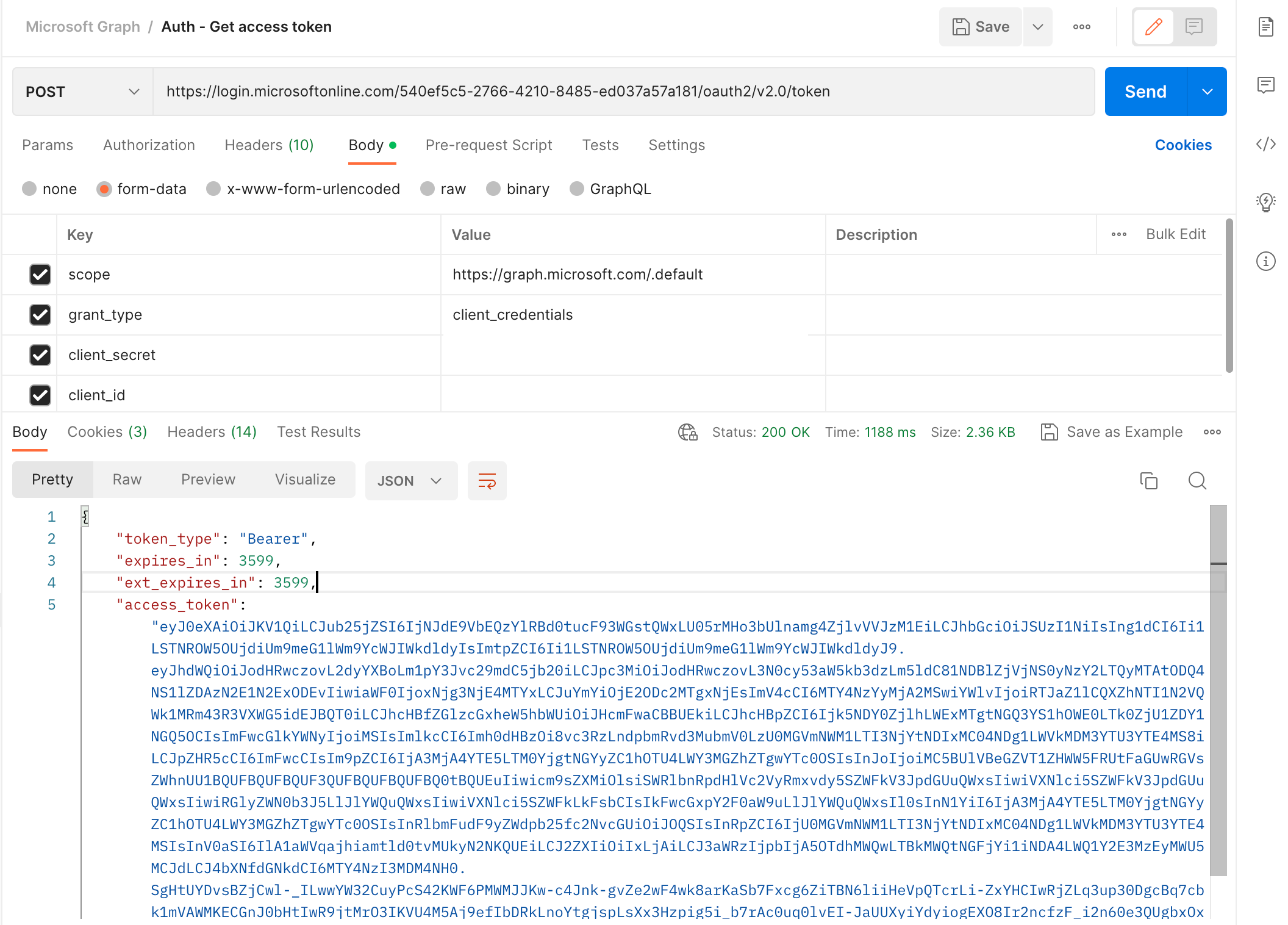
Open Postman and create a POST request to the following URL along with the appropriate parameters.
URL: https://login.microsoftonline.com/{b2c_tenant_id}/oauth2/v2.0/token
scope: https://graph.microsoft.com/.default
grant_type: client_credentials
client_secret: [Your client secret from the section above]
client_id: [Your client id from the section above]
Get the list of applications
Set the access_token generated from the above call as the Bearer Token authorization header parameter to create a GET request to the https://graph.microsoft.com/v1.0/applications endpoint. This endpoint will return a list of all the applications in this tenant.
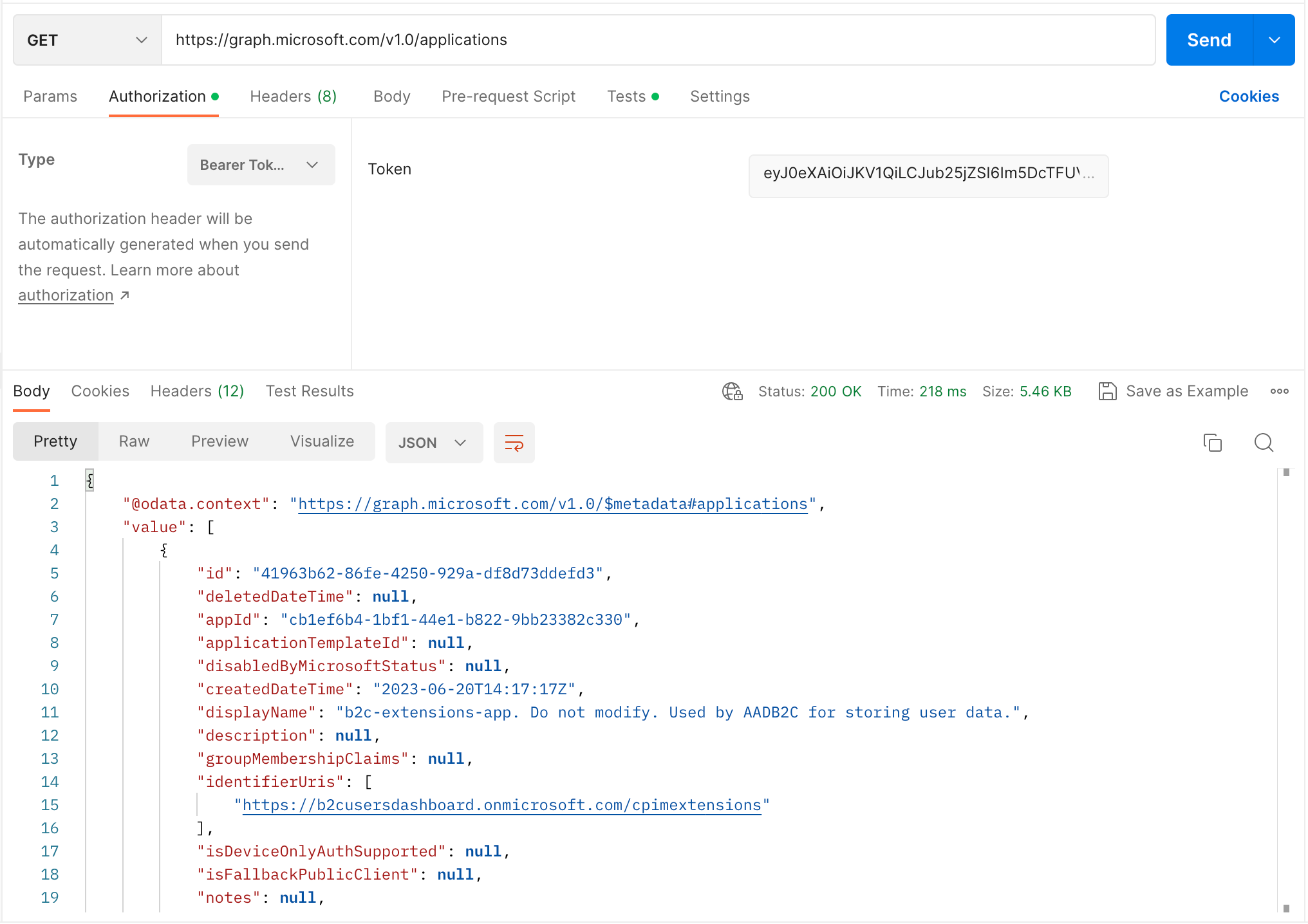
Find the application with the displayName equal to b2c-extensions-app. Do not modify. Used by AADB2C for storing user data and copy the id and appId property values. For some reason there are two different Id values for the application. In most cases with Azure B2C and AD we deal with the appId but in this case to get this application we need to use the id property.
List the all B2C extension properties of this application
Using the access_token and the id field from the previous call, create a GET request to the https://graph.microsoft.com/v1.0/applications/{id}/extensionProperties endpoint. This endpoint will return the list of all the extension properties that were created for this application. Here you can see that I have created an extension property called Role that is associated to the user object. The value property is an array, as you create more custom extensions they will populate this array.
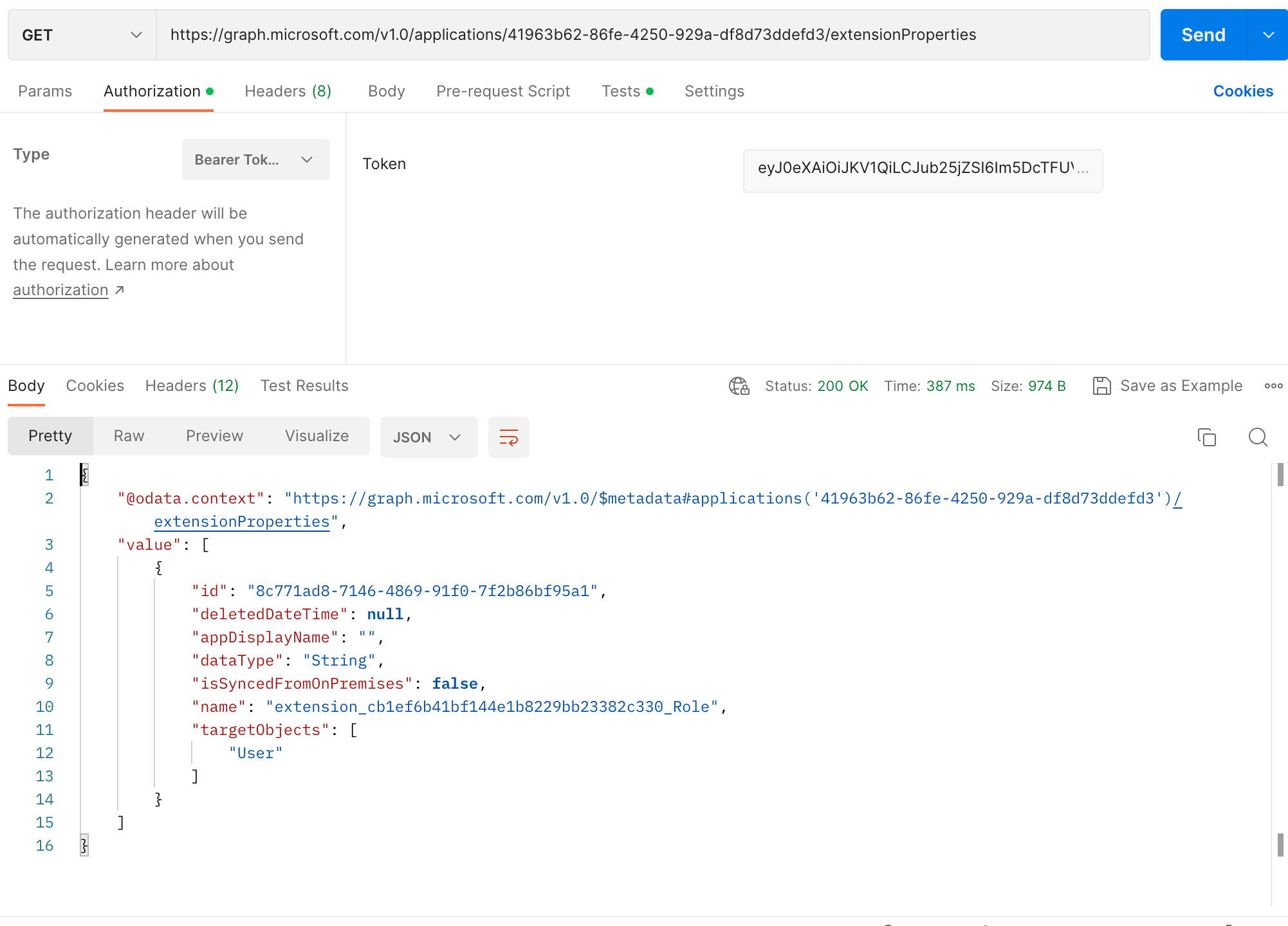
And in conclusion this is how you get a list of all extension attributes from a Azure B2C tenant using the MS Graph API. It's a little round about having to utilize the id property and not the appId property.